Excellent!
Computer Networks Security from Scratch to Advanced
Computer Networks Security Technologies and Tools for Network Admins and Cyber Security Officers

Lectures -52
Resources -51
Duration -8 hours
Lifetime Access

Lifetime Access
30-days Money-Back Guarantee
Get your team access to 10000+ top Tutorials Point courses anytime, anywhere.
Course Description
By the end of this course, you will be fully aware of the wired and wireless computer networks basics, devices, and protocols at a step-by-step pace. You will also reach a professional level in network security in terms of concepts, technologies, and tools. The course requires no background or pre-requisite, yet you will be able to understand all the up-to-date terminologies in network security during the lectures.
This course is organized as follows:
Section 1: Introduction to Computer Networks
- Lecture 1: What is a Computer Network?
- Lecture 2: Computer Networks Topologies
- Lecture 3: Computer Networks Categories
- Lecture 4: Computer Networks Devices and Services
- Lecture 5: Computer Networks Transmission Media
Section 2: ISO/OSI Model (7 Layers)
- Lecture 1: Why ISO/OSI Model?
- Lecture 2: Application, Presentation, and Session Layers
- Lecture 3: Transport and Network Layers
- Lecture 4: Data Link and Physical Layers
- Lecture 5: ISO/OSI Model in Action
Section 3: TCP/IP Protocol Suite
- Lecture 1: Introduction to Computer Networks Protocols
- Lecture 2: IP Protocol
- Lecture 3: TCP and UDP Protocols
- Lecture 4: Application Protocols
- Lecture 5: TCP/IP Characteristics and Tools
Section 4: Wireless Networks
- Lecture 1: Wireless Networks Benefits
- Lecture 2: Wireless Networks Types
- Lecture 3: Wireless Networks Protocol (Wi-Fi)
- Lecture 4: Wireless Networks Devices
- Lecture 5: Wireless Networks Drawbacks
Section 5: Computer Networks Security
- Lecture 1: Security Goals
- Lecture 2: Securing the Network Design
- Lecture 3: TCP/IP Security and Tools
- Lecture 4: Port Scanning and Tools
- Lecture 5: Sniffing and Tools
Section 6: Firewalls and Honeypots
- Lecture 1: Why Use a Firewall?
- Lecture 2: Firewalls Rules
- Lecture 3: Firewalls Filtering
- Lecture 4: Honey Pots
- Lecture 5: Bypassing Firewalls
Section 7: Intrusion Detection and Prevention Systems (IDS/IPS)
- Lecture 1: What are Intrusion Detection Systems (IDS)?
- Lecture 2: Network IDS (NIDS)
- Lecture 3: NIDS Challenges
- Lecture 4: Snort as NIDS
- Lecture 5: Intrusion Prevention Systems (IPS)
Section 8: Wireless Networks Security
- Lecture 1: Wired Equivalent Privacy WEP Attacking
- Lecture 2: WPA and AES Protocols
- Lecture 3: Wireless Security Misconceptions
- Lecture 4: Wireless Attacks and Mitigation
- Lecture 5: Secure Network Design with Wireless
Section 9: Physical Security & Incident Handling
- Lecture 1: Physical Security Objectives
- Lecture 2: Physical Threats and Mitigation
- Lecture 3: Defense in Depth (DiD)
- Lecture 4: What is an Incident?
- Lecture 5: Incident Handling
Section 10: Computer Networks Security Conclusion
- Lecture 1: Confidentiality, Integrity, and Availability (CIA)
- Lecture 2: Assets, Threats, and Vulnerabilities
- Lecture 3: Risks and Network Intrusion
- Lecture 4: Common Attacks
- Lecture 5: Security Recommendations
Who this course is for?
- Network administrators.
- Cyber security officers.
- Computer science undergraduates.
- Computer engineering undergraduates.
- Network security postgraduates.
- Network technical support specialists.
- Security incident handlers.
- IT Engineers and CEOs.
- Software Developers.
- Web Developers.
- Mobile Applications Developers.
Goals
- Introduction to Computer Networks.
- ISO/OSI Model (7 Layers).
- TCP/IP Protocol Suite.
- Wireless Networks.
- Computer Networks Security.
- Firewalls and Honeypots.
- Intrusion Detection and Prevention Systems (IDS/IPS).
- Wireless Networks Security.
- Physical Security & Incident Handling.
- Computer Networks Security Recommendations.
Prerequisites
- Basic computer knowledge.
- Basic Internet skills and adequate connection.
- Beginner networking background.
- Microsoft Windows machine.
- Microsoft PowerPoint for the presentation material.
- Beginner cyber security information.
- Laptop machine and standard browser.

Curriculum
Check out the detailed breakdown of what’s inside the course
Introduction to Computer Networks
6 Lectures
-
Introduction 09:57 09:57
-
What is a Computer Network? 10:29 10:29
-
Computer Networks Topologies 11:06 11:06
-
Computer Networks Categories 09:47 09:47
-
Computer Networks Devices and Services 10:38 10:38
-
Computer Networks Transmission Media 09:19 09:19
ISO/OSI Model (7 Layers)
5 Lectures

TCP/IP Protocol Suite
5 Lectures

Wireless Networks
5 Lectures

Computer Networks Security
5 Lectures

Firewalls and Honeypots
5 Lectures

Intrusion Detection and Prevention Systems (IDS/IPS)
5 Lectures

Wireless Networks Security
5 Lectures

Physical Security and Incident Handling
5 Lectures

Computer Networks Security Conclusion
5 Lectures

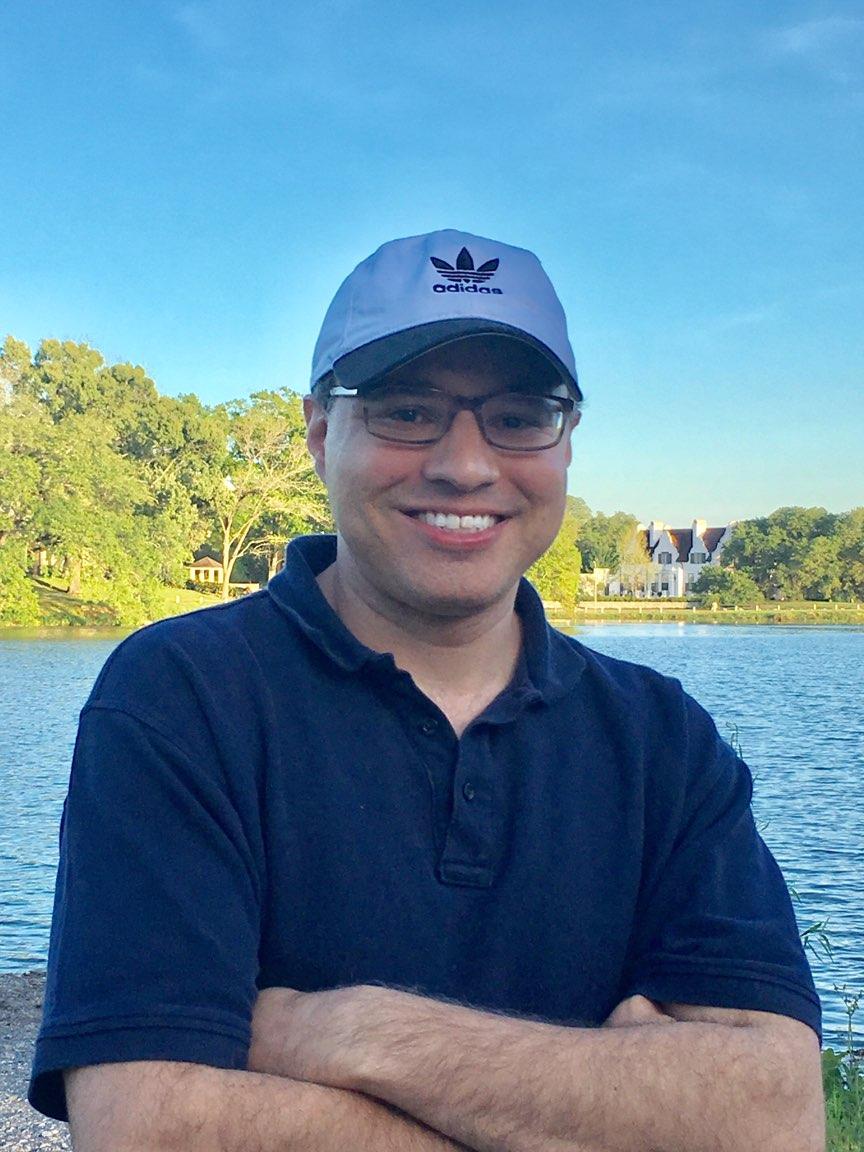
Instructor Details

Mohammad Adly
Education
Ph. D., “Enhanced Congestion Control for Internet Media Traffic”, Computer Engineering and Sciences Dept., Faculty of Electronic Engineering, Menoufiya University, 2006 - 2013.
M. Sc., “Video Services for Distant Work in an IP Environment”, Computer Engineering and Sciences Dept., Faculty of Electronic Engineering, Menoufiya University, 2002 - 2005.
Researcher, IRISA Institute, Rennes I University, France, 2001 - 2002.
Information Technology Diploma, Information Technology Institute ITI, Computer Networks Dept., 1998 - 1999.
B. Sc., Communications and Electronics Dept., Faculty of Engineering, Cairo University, 1993 - 1998.
Certificates
Lean Six Sigma Green Belt, SECC/ITIDA, April 2016.
Dale Carnegie Certified Instructor, 2015
GIAC Assessing Wireless Networks GAWN 617, SysAdmin, Audit, Network, Security SANS, 2010.
GIAC Certified Firewall Analyst GCFW 502, SysAdmin, Audit, Network, Security SANS, 2009.
GIAC Certified Incident Handler GCIH 504, SysAdmin, Audit, Network, Security SANS, 2009.
GIAC Security Essentials GSEC 401, SysAdmin, Audit, Network, Security SANS, 2009.
RITI Advanced Management Program RAMP, Regional Information Technology Institute RITI, 2008.
Publications
“Enhanced TCP-Friendly Rate Control for Supporting Video Traffic over Internet”, Mohammad A. Talaat, Gamal M. Attiya, and Magdi A. Koutb, Canadian Journal of Electrical and Computer Engineering CJECE, vol. 36, no. 4, 2013.
“ETFRC: Enhanced TFRC for Media Traffic over Internet”, International Journal of Computer Networks, IJCN, vol. 3, no. 3, pp. 167-177, August 2011.
“ETFRC: Enhanced TFRC for Media Traffic”, International Journal of Computer Applications, IJCA, vol. 18, no. 6, pp. 1-8, March 2011.
“PSNR Evaluation for Media Traffic over TFRC”, Mohammad A. Talaat, Magdi A. Koutb, and Hoda S. Sorour, International Journal of Computer Networks & Communications IJCNC, vol. 1, no. 3, pp. 71-76, October 2009.
“A Survey on Unicast Congestion Control Protocols for Media Traffic”, Mohammad A. Talaat, Magdi A. Koutb, and Hoda S. Sorour, International Journal of Computer Science and Network Security IJCSNS, vol. 9, no. 3, pp. 254-261, March 2009.
“Congestion Control for Internet Media Traffic”, Mohammad A. Talaat, Magdi A. Koutb, and Hoda S. Sorour, World Academy of Science, Engineering, and Technology WASET Proceedings, vol. 44, pp. 208-212, Venice, Italy, August 2008.
“Content-Aware Adaptive Video Streaming System”, Mohammad A. Talaat, Magdi A. Koutb, Hamdy M. Kelash, and Reda H. Aboelez. Published in the proceedings of the following conferences:
Information and Communications Technologies ICT 2005, Cape Town, South Africa, May 2005.
International Conference on Information and Communications Technologies ICICT 2005, Cairo, Egypt, Dec. 2005.
Course Certificate
Use your certificate to make a career change or to advance in your current career.

Our students work
with the Best






























Feedbacks
Related Video Courses
View MoreAnnual Membership
Become a valued member of Tutorials Point and enjoy unlimited access to our vast library of top-rated Video Courses
Subscribe now
Online Certifications
Master prominent technologies at full length and become a valued certified professional.
Explore Now


 Updated on Apr, 2026
Updated on Apr, 2026
 Language - English
Language - English